Degens Money Degenerates: Difference between revisions
No edit summary |
No edit summary |
||
| Line 1: | Line 1: | ||
{{Imported Case Study|source=https://www.quadrigainitiative.com/casestudy/degensmoneydegenerates.php}} | {{Imported Case Study 2|source=https://www.quadrigainitiative.com/casestudy/degensmoneydegenerates.php}} | ||
{{Unattributed Sources}} | {{Unattributed Sources}} | ||
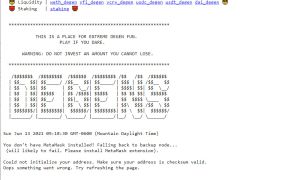
[[File:Degensmoney.jpg|thumb|Degens Money]]The Degens Money platform was experimental in nature and required users to click past a number of warnings, at which point they gave full access to their ethereum wallet (and any held ERC20 tokens) to the platform. Once connected up, there was no easy way to revoke the granted permissions. Users had to follow the set of instructions written by another third party. | [[File:Degensmoney.jpg|thumb|Degens Money]]The Degens Money platform was experimental in nature and required users to click past a number of warnings, at which point they gave full access to their ethereum wallet (and any held ERC20 tokens) to the platform. Once connected up, there was no easy way to revoke the granted permissions. Users had to follow the set of instructions written by another third party. | ||
This is a global/international case not involving a specific country. | This is a global/international case not involving a specific country.<ref name="kalis-1097" /><ref name="nomosparadoxtwitter-1313" /><ref name="coinness-1314" /><ref name="degensmoneytwitter-1315" /><ref name="blockcast-1316" /><ref name="degensmoney-1317" /><ref name="degensmoneymedium-1318" /><ref name="bscdotnews-1319" /><ref name="blockcast-1151" /><ref name="slowmisthacked-678" /><ref name="blocksecteammedium-3714" /><ref name="nomosparadoxtwitter-3721" /><ref name="secos-3722" /> | ||
<ref name="kalis-1097" /><ref name="nomosparadoxtwitter-1313" /><ref name="coinness-1314" /><ref name="degensmoneytwitter-1315" /><ref name="blockcast-1316" /><ref name="degensmoney-1317" /><ref name="degensmoneymedium-1318" /><ref name="bscdotnews-1319" /><ref name="blockcast-1151" /><ref name="slowmisthacked-678" /><ref name="blocksecteammedium-3714" /><ref name="nomosparadoxtwitter-3721" /><ref name="secos-3722" /> | |||
== About Degens Money == | == About Degens Money == | ||
| Line 59: | Line 58: | ||
!Description | !Description | ||
|- | |- | ||
|August 27th, 2020 | |August 27th, 2020 | ||
|Main Event | |Main Event | ||
|Expand this into a brief description of what happened and the impact. If multiple lines are necessary, add them here. | |Expand this into a brief description of what happened and the impact. If multiple lines are necessary, add them here. | ||
| Line 67: | Line 66: | ||
| | | | ||
|} | |} | ||
== Technical Details == | |||
This section includes specific detailed technical analysis of any security breaches which happened. What specific software vulnerabilities contributed to the problem and how were they exploited? | |||
== Total Amount Lost == | == Total Amount Lost == | ||
| Line 86: | Line 88: | ||
== Ongoing Developments == | == Ongoing Developments == | ||
What parts of this case are still remaining to be concluded? | What parts of this case are still remaining to be concluded? | ||
== General Prevention Policies == | |||
== Prevention Policies == | |||
In terms of the smart contract, this case involved unlimited permissions being granted, which is highly dangerous and exposed investors to risks they might not have realized beyond a standard liquidity pool. The vulnerable contract had not even been audited. | In terms of the smart contract, this case involved unlimited permissions being granted, which is highly dangerous and exposed investors to risks they might not have realized beyond a standard liquidity pool. The vulnerable contract had not even been audited. | ||
In general, smart contracts have a security profile similar to hot wallets. Human beings have a much stronger track record of detecting breaches, and a multi-sig of known individuals is generally safer than a smart contract. | In general, smart contracts have a security profile similar to hot wallets. Human beings have a much stronger track record of detecting breaches, and a multi-sig of known individuals is generally safer than a smart contract. | ||
== Individual Prevention Policies == | |||
{{Prevention:Individuals:Placeholder}} | |||
{{Prevention:Individuals:End}} | |||
== Platform Prevention Policies == | |||
{{Prevention:Platforms:Placeholder}} | |||
{{Prevention:Platforms:End}} | |||
== Regulatory Prevention Policies == | |||
{{Prevention:Regulators:Placeholder}} | |||
{{Prevention:Regulators:End}} | |||
== References == | == References == | ||
<references><ref name="kalis-1097">[https://kalis.me/unlimited-erc20-allowances/ Unlimited ERC20 allowances considered harmful] (Jun | <references><ref name="kalis-1097">[https://kalis.me/unlimited-erc20-allowances/ Unlimited ERC20 allowances considered harmful] (Jun 5, 2021)</ref> | ||
<ref name="nomosparadoxtwitter-1313">[https://twitter.com/nomos_paradox/status/1299215849018937345 @nomos_paradox Twitter] (Jun | <ref name="nomosparadoxtwitter-1313">[https://twitter.com/nomos_paradox/status/1299215849018937345 @nomos_paradox Twitter] (Jun 5, 2021)</ref> | ||
<ref name="coinness-1314">[https://www.coinness.com/news/744264 Degen.Money Is Exposed To Obtain User Funds Through Double Approval | CoinNess] (Jun | <ref name="coinness-1314">[https://www.coinness.com/news/744264 Degen.Money Is Exposed To Obtain User Funds Through Double Approval | CoinNess] (Jun 13, 2021)</ref> | ||
<ref name="degensmoneytwitter-1315">[https://twitter.com/DegensMoney/status/1299233255812628480 @DegensMoney Twitter] (Jun | <ref name="degensmoneytwitter-1315">[https://twitter.com/DegensMoney/status/1299233255812628480 @DegensMoney Twitter] (Jun 13, 2021)</ref> | ||
<ref name="blockcast-1316">[https://blockcast.cc/news/chengdu-lianan-in-august-there-were-5-security-incidents-in-the-defi-field-and-a-total-of-39-incidents-in-the-blockchain-field/ Chengdu Lianan: In August, there were 5 security incidents in the DeFi field, and a total of 39 incidents in the blockchain field • Blockcast.cc- News on Blockchain, DLT, Cryptocurrency] (Jun | <ref name="blockcast-1316">[https://blockcast.cc/news/chengdu-lianan-in-august-there-were-5-security-incidents-in-the-defi-field-and-a-total-of-39-incidents-in-the-blockchain-field/ Chengdu Lianan: In August, there were 5 security incidents in the DeFi field, and a total of 39 incidents in the blockchain field • Blockcast.cc- News on Blockchain, DLT, Cryptocurrency] (Jun 13, 2021)</ref> | ||
<ref name="degensmoney-1317">[https://degens.money/ Degens Money] (Jun | <ref name="degensmoney-1317">[https://degens.money/ Degens Money] (Jun 13, 2021)</ref> | ||
<ref name="degensmoneymedium-1318">[https://medium.com/degens-money/degens-money-for-pure-degen-fun-4140acdc7c0d Degens Money For Pure Degen Fun] (Jun | <ref name="degensmoneymedium-1318">[https://medium.com/degens-money/degens-money-for-pure-degen-fun-4140acdc7c0d Degens Money For Pure Degen Fun] (Jun 13, 2021)</ref> | ||
<ref name="bscdotnews-1319">[https://www.bsc.news/post/dive-into-de-fi-dont-be-a-degen Dive Into De-Fi: Don't Be A Degen] (Jun | <ref name="bscdotnews-1319">[https://www.bsc.news/post/dive-into-de-fi-dont-be-a-degen Dive Into De-Fi: Don't Be A Degen] (Jun 20, 2021)</ref> | ||
<ref name="blockcast-1151">[https://blockcast.cc/news/what-are-the-possible-security-risks-of-unlimited-token-authorization/ What are the possible security risks of unlimited token authorization? • Blockcast.cc- News on Blockchain, DLT, Cryptocurrency] (Jun | <ref name="blockcast-1151">[https://blockcast.cc/news/what-are-the-possible-security-risks-of-unlimited-token-authorization/ What are the possible security risks of unlimited token authorization? • Blockcast.cc- News on Blockchain, DLT, Cryptocurrency] (Jun 20, 2021)</ref> | ||
<ref name="slowmisthacked-678">[https://hacked.slowmist.io/en/?c=ETH%20DApp SlowMist Hacked - SlowMist Zone] (May | <ref name="slowmisthacked-678">[https://hacked.slowmist.io/en/?c=ETH%20DApp SlowMist Hacked - SlowMist Zone] (May 18, 2021)</ref> | ||
<ref name="blocksecteammedium-3714">[https://blocksecteam.medium.com/unlimited-approval-in-erc20-convenience-or-security-1c8dce421ed7 Unlimited Approval In Erc20 Convenience Or Security] (Oct | <ref name="blocksecteammedium-3714">[https://blocksecteam.medium.com/unlimited-approval-in-erc20-convenience-or-security-1c8dce421ed7 Unlimited Approval In Erc20 Convenience Or Security] (Oct 12, 2021)</ref> | ||
<ref name="nomosparadoxtwitter-3721">[https://blocksecteam.medium.com/all_projects/ethscope/Approval/defcon/-/blob/master/twitter.com/nomos_paradox/status/1299215849018937345 https://blocksecteam.medium.com/all_projects/ethscope/Approval/defcon/-/blob/master/twitter.com/nomos_paradox/status/1299215849018937345] (Oct | <ref name="nomosparadoxtwitter-3721">[https://blocksecteam.medium.com/all_projects/ethscope/Approval/defcon/-/blob/master/twitter.com/nomos_paradox/status/1299215849018937345 https://blocksecteam.medium.com/all_projects/ethscope/Approval/defcon/-/blob/master/twitter.com/nomos_paradox/status/1299215849018937345] (Oct 12, 2021)</ref> | ||
<ref name="secos-3722">[https://git.secos.mobi:9930/all_projects/ethscope/Approval/defcon/-/blob/master/kalis.me/unlimited-erc20-allowances https://git.secos.mobi:9930/all_projects/ethscope/Approval/defcon/-/blob/master/kalis.me/unlimited-erc20-allowances] (Oct | <ref name="secos-3722">[https://git.secos.mobi:9930/all_projects/ethscope/Approval/defcon/-/blob/master/kalis.me/unlimited-erc20-allowances https://git.secos.mobi:9930/all_projects/ethscope/Approval/defcon/-/blob/master/kalis.me/unlimited-erc20-allowances] (Oct 12, 2021)</ref></references> | ||
Latest revision as of 10:16, 2 May 2023
Notice: This page is a freshly imported case study from the original repository. The original content was in a different format, and may not have relevant information for all sections. Please help restructure the content by moving information from the 'About' and 'General Prevention' sections to other sections, and add any missing information or sources you can find. If you are new here, please read General Tutorial on Wikis or Anatomy of a Case Study for help getting started.
Notice: This page contains sources which are not attributed to any text. The unattributed sources follow the initial description. Please assist by visiting each source, reviewing the content, and placing that reference next to any text it can be used to support. Feel free to add any information that you come across which isn't present already. Sources which don't contain any relevant information can be removed. Broken links can be replaced with versions from the Internet Archive. See General Tutorial on Wikis, Anatomy of a Case Study, and/or Citing Your Sources Guide for additional information. Thanks for your help!
The Degens Money platform was experimental in nature and required users to click past a number of warnings, at which point they gave full access to their ethereum wallet (and any held ERC20 tokens) to the platform. Once connected up, there was no easy way to revoke the granted permissions. Users had to follow the set of instructions written by another third party.
This is a global/international case not involving a specific country.[1][2][3][4][5][6][7][8][9][10][11][12][13]
About Degens Money
"A PLACE FOR EXTREME DEGEN FUN. PLAY IF YOU DARE." "Degens.money is created for ultimate and pure degen fun. $DEGEN is the yield farming token to end all yield farming tokens."
"Most of the code are forked from existing protocols such as Compound, Synthetix, which have been running on mainnet without known issues. We encourage you to do your own due diligence before playing." "WARNING: DO NOT INVEST AN AMOUNT YOU CANNOT LOSE."
"Another such case happened with a project called Degen Money, which used a slightly less sophisticated (but not less effective) approach. Rather than developing their own smart contract, they created a frontend that made two approval transactions. One to a functioning contract, and one to a completely different address. Because many people do not specifically check the contract addresses, this allowed the attackers to drain users' wallets."
A Twitter user named Nik Kunkel tweeted: "Funds are not SAFU (Degen.Money). Anyone who used the UX for yield farming is exposed to a double approval exploit. The first approval is for the staking contract, the second approval lets the attacker pull that token from your wallet!" YFI founder Andre Cronje commented on this tweet, saying, "I've confirmed this is accurate. They are approving your funds to themselves, they are currently using transferFrom to take funds from users. Please revoke approvals, withdrawing your funds is not sufficient."
"Anyone who used the UX for yieldfarming is exposed to a double approval exploit. The first approval is for the staking contract, the second approval lets the attacker pull that token from your wallet!"
"Push unique friends broke the news, DeFi liquidity mining project Degen.Money use dual licensing loopholes (Double Approval Exploit) to obtain the user money. YFI founder Andre Cronje also said on Twitter that the project is indeed risky and requires manual cancellation of authorization."
"A malicious approve bug has been found in our UI code. Please do not use http://degens.money for any action until further notice. You can follow https://twitter.com/nomos_paradox/status/1299215849018937345 to undo the malicious approvals. We sincerely apologize for this incident."
"Twitter users reported that DeFi's liquidity mining project Degen.Money exploited a double approval vulnerability to get users' Money. The first authorization gives the pledge contract, and the second authorization gives the right to transfer money, which will result in the user's funds being taken away by the attacker. YFI founder Andre Cronje says the project does have risks."
This is a global/international case not involving a specific country.
The background of the exchange platform, service, or individuals involved, as it would have been seen or understood at the time of the events.
Include:
- Known history of when and how the service was started.
- What problems does the company or service claim to solve?
- What marketing materials were used by the firm or business?
- Audits performed, and excerpts that may have been included.
- Business registration documents shown (fake or legitimate).
- How were people recruited to participate?
- Public warnings and announcements prior to the event.
Don't Include:
- Any wording which directly states or implies that the business is/was illegitimate, or that a vulnerability existed.
- Anything that wasn't reasonably knowable at the time of the event.
There could be more than one section here. If the same platform is involved with multiple incidents, then it can be linked to a main article page.
The Reality
This sections is included if a case involved deception or information that was unknown at the time. Examples include:
- When the service was actually started (if different than the "official story").
- Who actually ran a service and their own personal history.
- How the service was structured behind the scenes. (For example, there was no "trading bot".)
- Details of what audits reported and how vulnerabilities were missed during auditing.
What Happened
The specific events of the loss and how it came about. What actually happened to cause the loss and some of the events leading up to it.
| Date | Event | Description |
|---|---|---|
| August 27th, 2020 | Main Event | Expand this into a brief description of what happened and the impact. If multiple lines are necessary, add them here. |
Technical Details
This section includes specific detailed technical analysis of any security breaches which happened. What specific software vulnerabilities contributed to the problem and how were they exploited?
Total Amount Lost
The total amount lost is unknown.
How much was lost and how was it calculated? If there are conflicting reports, which are accurate and where does the discrepancy lie?
Immediate Reactions
How did the various parties involved (firm, platform, management, and/or affected individual(s)) deal with the events? Were services shut down? Were announcements made? Were groups formed?
Ultimate Outcome
What was the end result? Was any investigation done? Were any individuals prosecuted? Was there a lawsuit? Was any tracing done?
Total Amount Recovered
There do not appear to have been any funds recovered in this case.
What funds were recovered? What funds were reimbursed for those affected users?
Ongoing Developments
What parts of this case are still remaining to be concluded?
General Prevention Policies
In terms of the smart contract, this case involved unlimited permissions being granted, which is highly dangerous and exposed investors to risks they might not have realized beyond a standard liquidity pool. The vulnerable contract had not even been audited.
In general, smart contracts have a security profile similar to hot wallets. Human beings have a much stronger track record of detecting breaches, and a multi-sig of known individuals is generally safer than a smart contract.
Individual Prevention Policies
No specific policies for individual prevention have yet been identified in this case.
For the full list of how to protect your funds as an individual, check our Prevention Policies for Individuals guide.
Platform Prevention Policies
Policies for platforms to take to prevent this situation have not yet been selected in this case.
For the full list of how to protect your funds as a financial service, check our Prevention Policies for Platforms guide.
Regulatory Prevention Policies
No specific regulatory policies have yet been identified in this case.
For the full list of regulatory policies that can prevent loss, check our Prevention Policies for Regulators guide.
References
- ↑ Unlimited ERC20 allowances considered harmful (Jun 5, 2021)
- ↑ @nomos_paradox Twitter (Jun 5, 2021)
- ↑ Degen.Money Is Exposed To Obtain User Funds Through Double Approval | CoinNess (Jun 13, 2021)
- ↑ @DegensMoney Twitter (Jun 13, 2021)
- ↑ Chengdu Lianan: In August, there were 5 security incidents in the DeFi field, and a total of 39 incidents in the blockchain field • Blockcast.cc- News on Blockchain, DLT, Cryptocurrency (Jun 13, 2021)
- ↑ Degens Money (Jun 13, 2021)
- ↑ Degens Money For Pure Degen Fun (Jun 13, 2021)
- ↑ Dive Into De-Fi: Don't Be A Degen (Jun 20, 2021)
- ↑ What are the possible security risks of unlimited token authorization? • Blockcast.cc- News on Blockchain, DLT, Cryptocurrency (Jun 20, 2021)
- ↑ SlowMist Hacked - SlowMist Zone (May 18, 2021)
- ↑ Unlimited Approval In Erc20 Convenience Or Security (Oct 12, 2021)
- ↑ https://blocksecteam.medium.com/all_projects/ethscope/Approval/defcon/-/blob/master/twitter.com/nomos_paradox/status/1299215849018937345 (Oct 12, 2021)
- ↑ https://git.secos.mobi:9930/all_projects/ethscope/Approval/defcon/-/blob/master/kalis.me/unlimited-erc20-allowances (Oct 12, 2021)